For details, see:
Mark files and events as evidence in
When you discover information that's critical to your conclusions, you can mark it as evidence in your investigation. Evidence can include files, artifacts, action results, events, and notes. Tagging evidence helps to separate general information from information that's directly related to diagnosing an incident. All evidence appears on the Evidence tab within an investigation.
Mark a file as evidence
Perform the following steps to mark a file as evidence:
- Navigate to a container in .
- Click Analyst to change the container to analyst view.
- Click the Files tab.
- Click the
 more icon for the file.
more icon for the file. - Select Mark as Evidence.
- Click Confirm.
Mark an event as evidence
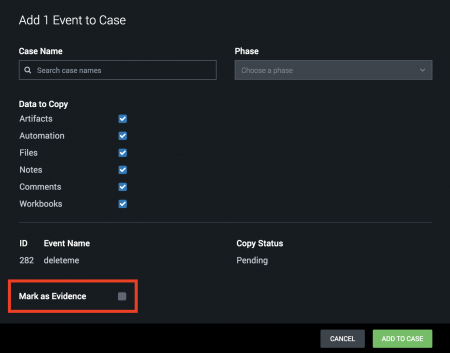
To mark an event as evidence, select Mark as Evidence when adding the event to a case. For more information about adding events to cases, see Add objects to a case in . The following screenshot illustrates how to mark an event as evidence.
When you add an event to an existing case, it copies all the data from the existing event into the case you're adding it to while also maintaining the original event data. The information on the Evidence tab is a copy of the original event, not the actual event.
| Add files to an event in | View recommended playbooks, actions, and mission experts for resolving an event |
This documentation applies to the following versions of Splunk® SOAR (On-premises): 5.1.0, 5.2.1, 5.3.1, 5.3.2, 5.3.3, 5.3.4, 5.3.5, 5.3.6, 5.4.0, 5.5.0, 6.0.0, 6.0.1, 6.0.2, 6.1.0, 6.1.1, 6.2.0, 6.2.1, 6.2.2, 6.3.0, 6.3.1, 6.4.0, 6.4.1
 Download manual
Download manual
Feedback submitted, thanks!